March 2, 2026
How a “Wrong Number” Text Turned Into a Million-Dollar Crypto Scam
How a “Wrong Number” Text Turned Into a Million-Dollar Crypto Scam
How a “Wrong Number” Text Turned Into a Million-Dollar Crypto Scam
Recently, I was pulled into a real-world crypto situation that quickly escalated from “this seems odd” to tracing a multi-million-dollar laundering wallet on the blockchain.
● This wasn’t amateur.
● This was structured infrastructure.
And it started with a simple text message
It Began With “Is This Holly?”
The first message read:
“Is that you Holly?”
Wrong number.
A polite response led to conversation.
The profile was polished:
● Attractive, sandy-haired blond
● Professional lifestyle photos
● Detailed backstory
● Balanced personal and slightly intimate responses
● Daily check-ins
Nothing felt aggressive.
Trust was built slowly. Carefully. Deliberately.
This is relationship engineering — and it is the foundation of many modern crypto scams.
The Introduction of the “Financial Advisor”
Once emotional trust was established, the next layer was introduced.
A “financial advisor.”
● Professional website.
● Clean design.
● Investment language.
● References to a published book.
● Credential claims.
The identity had been stolen from a real financial professional.
The trading dashboard looked legitimate:
● Real-time charts
● Account balances
● Profit history
● Clean interface
My friend was told:
“You are not a novice at crypto trading… you are an EXPERT.”
That praise was intentional.
The data was fake.
But the confidence it created was real.
The account appeared to grow to over $300,000.
Then the Lockout
Without warning, access was blocked. Withdrawals were frozen. Then came escalation.
An email appeared — impersonating the SEC.
It demanded a $20,000 crypto deposit to “verify compliance” and prove he was not engaging in fraud because his trading performance was “too successful.”
The narrative flipped.
The victim now had to prove he wasn’t the criminal.
Then came additional pressure:
● 1.5% daily compounding penalties
● Loan enforcement language
● Legal escalation warnings
● 48-hour deadlines
● Threats of permanent account forfeiture
The psychological pressure increased rapidly.
That’s when he finally called me.
Initial Technical Review
The website fraud was easy to detect:
● Recently registered domain
● Hosting inconsistencies
● Credential misuse
● Government impersonation red flags
But the real truth is not on the website.
It’s on the blockchain.
The Transaction Hash
When cryptocurrency is sent from Coinbase (or any exchange), a transaction hash is generated. This is a permanent public record stored on the blockchain.
● It cannot be altered.
● It cannot be deleted.
● It cannot be faked.
I pulled the transaction hash from his Coinbase account.
From there, everything became clear.
● The funds were not being traded.
● They were immediately transferred to another wallet.
● Then forwarded again.
● Then routed through additional intermediary wallets.
● Finally, they were consolidated into a central aggregation wallet.
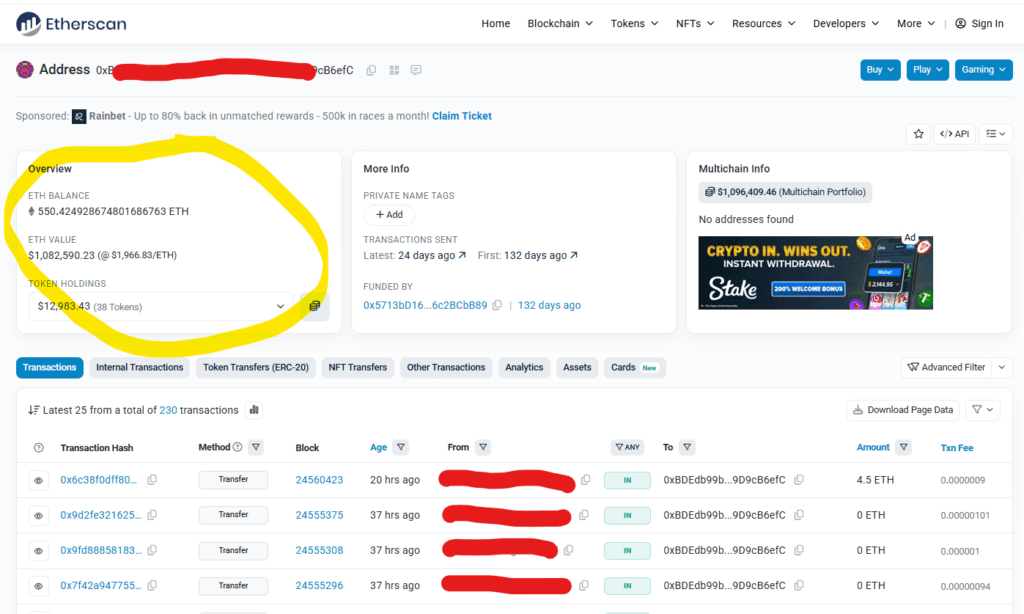
That wallet — shown in the attached screenshot — held over $1,000,000 in ETH at the time of review.
The bridge address in the screenshot has been intentionally covered for responsible disclosure.
This wallet has processed hundreds of similar transfers.
This is not a random scammer. This is operational infrastructure.
How the Laundering Structure Works (Simplified)
The pattern was consistent:
1. Victim sends crypto to a “trading” wallet.
2. Funds are immediately moved to an operational wallet.
3. Funds are forwarded through multiple intermediary wallets.
4. They are consolidated into a pooling wallet.
From there, assets can be:
● Bridged to other chains
● Split into smaller transactions
● Sent to exchanges
● Converted to other assets
The trading dashboard is theater. The blockchain is reality.
The Hard Truth
Crypto transactions are irreversible once confirmed.
Yes, they are traceable. But traceable does not mean recoverable. Blockchain shows wallet addresses — not identities.
To prosecute, authorities must:
● Identify operators
● Establish jurisdiction
● Coordinate internationally
● Gain cooperation from foreign agencies
Very often these operations are run outside the United States.
Even when funds are traceable, enforcement is extremely difficult.
In this case, the funds are unrecoverable.
Who They Target
If you:
● Own a business
● Manage retirement funds
● Have investment capital
● Control liquidity
You are a preferred target.
These operations prey on:
● Lack of technical knowledge
● Carefully engineered greed
The belief that:
“This could change everything.”
These scammers are not some kid sitting in a coffee shop.
They are structured, well-funded, multi-million-dollar operations investing heavily in:
● Professional websites
● Identity theft
● Psychological scripting
● Fake trading dashboards
● Crypto wallet infrastructure
● Laundering networks
The million-dollar wallet we traced is proof of scale.
What You Should Do
Start at the root.
● Do not respond to unknown messages — even if they sound polite or accidental.
● Do not engage with “wrong number” conversations. They are common entry points.
● Never send money to unlock money. No legitimate regulator demands crypto deposits.
● Never act under urgency, flattery, or fear. Those are tools.
● Always involve a technical second opinion before moving large sums.
● Pause before you send. Not after.
Final Thoughts
By the time doubt appears, the infrastructure has already done its job.
● The website looks real.
● The advisor sounds professional.
● The SEC email feels intimidating.
● The profits appear impressive.
● But the blockchain does not lie.
If you are a business owner or managing retirement assets, you are not outside the target list.
You are the target.
If something feels slightly off — verify before you trust.
And please share this with elderly friends, business owners, and anyone managing significant assets.
Frankly, I would rather they avoid these scams entirely than have to call me to dig them out of one.
Author
Dan Harley, II
Latest Episodes
Scammer Picked the Wrong Guy to Call | Energy-Saving Contractor Scam Exposed
https://youtu.be/IKlBJsLo3bc?si=ogBJg_hSAUtPtV4T A Scammer Who Picked the Wrong Guy Most people think scam calls are just an annoyance.A quick hang-up.A nuisance you forget about. But for millions of seniors — and
The Maverick Company Story — How One Small Fix Revived a Real Estate Empire
https://youtu.be/baRrFN-jQ8I A Comeback Story from the Mojave Desert Every business has its ups and downs. Some ride the wave. Some struggle.And some — with the right guidance — transform completely.
Windows 10 Is Ending — What You Need to Know Before It’s Too Late
https://youtu.be/Buia0JDs3GU?si=HdiN8Sla7yCzRRNd Windows 10 Is Ending — What You Need to Know Before It’s Too Late By Dan Harley IICategory: Tech Talk Series Windows 10 Is Retiring — Are You
Tech Talk #173 – Comparing RingCentral to Ooma VoIP Phone Systems
https://www.youtube.com/watch?v=WSuf1TNH3rgTech Talk #173 – Comparing RingCentral to Ooma VoIP Phone Systems I compare my old RingCentral VoIP service to my new Ooma VoIP phone system. Review the desktop apps and back
Tags
Leave a Reply Cancel reply
You must be logged in to post a comment.
This site uses Akismet to reduce spam. Learn how your comment data is processed.




